

The German Federal Office for Information Security (BSI) speaks of an "extremely critical threat situation": The Log4Shell vulnerability opens the floodgates to attackers on the network. It is keeping users and developers on their toes worldwide. IT expert Cristian Avram from Bitdefender speaks plainly in an interview: "The worst-case scenario has occurred."
The BSI's warning level is set to red. The Log4Shell IT security vulnerability poses a major threat to companies in particular. Accordingly, the interest at the digital After Work Talk of "it-sa 365" was great. Around 150 participants were informed and advised by IT experts Michael Gisevius and Cristian Avram on this burning issue.
At the dialog platform it-sa 365, IT security providers and experts network all year round and inform themselves about hardware, services as well as IT security solutions. Between the dates of it-sa, Europe's largest trade fair for IT security in Nuremberg, the online platform also offers a market overview and provides industry knowledge, professional articles and interviews.
Mr. Avram, please explain in general terms: What is Log4Shell?
To be clear, Log4Shell is the worst-case scenario that security experts have been warning about for years. Imagine you live in an area with a high crime rate and from one moment to the next you learn that all door locks are broken and criminals can easily enter your house. This is more or less the situation we find ourselves in.
What does Log4Shell stand for?
Log4Shell refers to a vulnerability that was identified in December last year. Log4j is an open source framework. Wherever users and developers use this Java library, the vulnerability is present. The doors into IT are potentially open for now!

Für Cristian Avram, IT-Sicherheitsexperte von Bitdefender, ist Log4Shell das "Worst-Case-Szenario".
The experts refer to this as a zero-day vulnerability. What is meant by this?
A zero-day vulnerability is the result of faulty programming code that the developers have unintentionally included. Attackers exploit this even before the developers have been able to fix the error.
How great is the danger from the hackers?
The threat level is very high. Because Log4j's open source code is freely available and very useful, it has become the de facto standard. It can be found in countless servers and services. Particularly dangerous: Many responsible parties may not even know where and for what they are using it.
Many hackers have probably already sneaked in and are lying in wait in their victims' networks.
What do the hackers' attacks look like?
Hackers are already exploiting the vulnerability in many ways. For example, our experts at Bitdefender have observed ransomware attacks or attempted implementations of cryptominers. Many hackers have probably already snuck in and are lying in wait in the network of the victim companies. As a result, many more attacks are sure to take place in the coming months. Some will be noticed, others will not.
How can you protect yourself?
Currently, the first thing you can do is update the vulnerability if you have located it in your IT. In addition, administrators should keep a particularly close eye on their systems in the near future. Attackers will have already infiltrated through the gap.
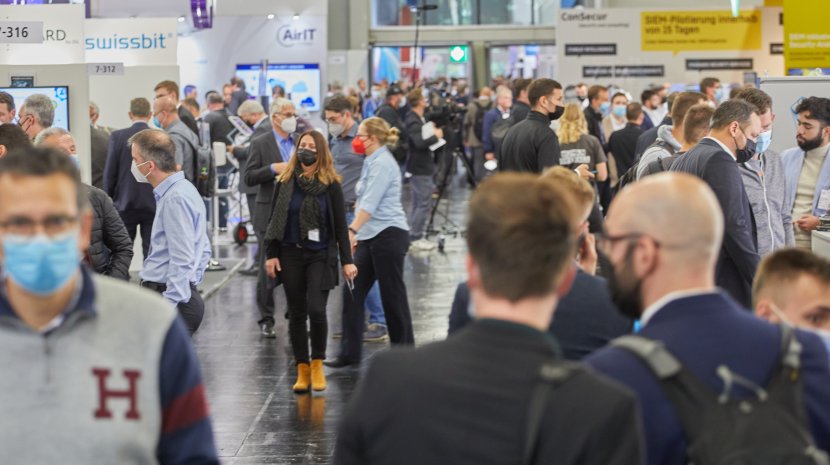
Europas größte Fachmesse für IT-Security findet jährlich in Nürnberg statt. In der Zwischenzeit vernetzen sich die Expertinnen und Experten auf der Plattform "it-sa 365".
Mr Avram, you are a Solutions Architect at Bitdefender. What exactly do you do and what solutions can you offer companies?
As a Solutions Architect, I advise and support customers in designing and building a secure IT infrastructure using our technologies. With our platform, companies can identify and respond to cyber threats at an early stage.
As an expert, how important is a platform like it-sa 365 for you?
it-sa 365 offers us the opportunity to get in touch with our customers and partners not only during a limited period of time like at an on-site trade show, but throughout the year. It is a useful additional platform for staying in dialog beyond the days of the trade show.
And how can the it-sa trade show in October top that?
Nothing beats the direct conversation! The on-site stand discussion at it-sa simply offers more personal contact and a more intensive exchange of higher quality.
Thank you very much for the interview, Mr Avram!
Current IT security-related topics can be found regularly at it-sa 365 - especially at the digital IT Security Talks from March 15-16, 2022.



